The CCNI Lab is not just a research facility; it's an innovation hub where brilliant minds unite to address pressing challenges in computational science and cybersecurity. Through cutting-edge research, hands-on experimentation, and collaborations with industry and government partners, we are driving technological advancements. Explore our research, meet our exceptional team, and join us in shaping a more secure, intelligent, and interconnected world.
Selected Research Projects
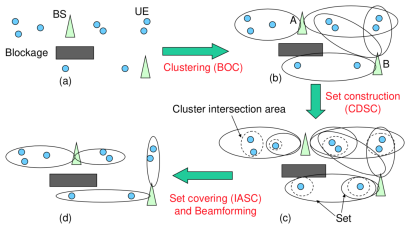
Energy Efficient Beamforming Optimization for 5G mmWave Networks
The millimeter wave (mmWave) frequency band is a promising candidate for next generation cellular and wireless networks. To compensate the significantly higher path loss due to the higher frequency, the mmWave band usually uses the beamforming technology. However, this makes the network topology control a great challenge. We propose a novel framework for network topology control in mmWave networks, termed Beamforming Oriented tOpology coNtrol (BOON). The objective is to reduce total transmit power of base stations and interference between beams. BOON smartly groups nearby user equipment into clusters, constructs sets from user equipment clusters, and associates user equipment to base stations and beams. On average BOON uses only 10%, 32%, and 25% transmit power of three state-of-the-art schemes in the literature, respectively, to achieve the same network sum rate.
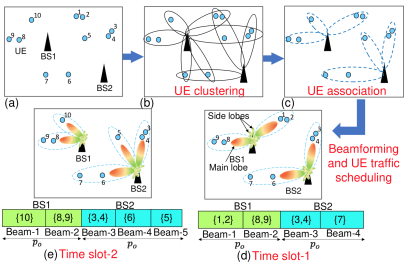
User Association and Scheduling for 5G mmWave networks
The millimeter wave (mmWave) band offers vast bandwidth and plays a key role for next generation wireless networks. However, the mmWave network raises a great challenge for user association and scheduling, due to the limited power budget and beamformers, diverse user traffic loads, user quality of service requirement, etc. We propose a novel framework for user association and scheduling in multi-base station mmWave networks, termed the clustering Based dOwnlink UE assOciation, Scheduling, beamforming with power allocaTion (BOOST). The objective is to reduce the downlink network transmission time, subject to the base station power budget, number of beamformers, user traffic loads, and the quality of service requirement at users. On average, BOOST reduces the transmission time by 37%, 30%, and 26%, and achieves a sum rate gain of 56%, 43%, and 34%, respectively, compared with three state-of-the-art schemes in the literature.
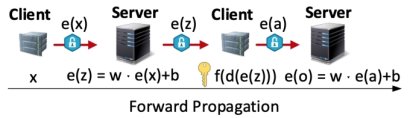
Privacy is a fundamental challenge for a variety of smart applications that depend on data aggregation and collaborative learning across different entities. We develop a novel privacy-preserved architecture where clients can collaboratively train a deep learning model while preserving the privacy of each client's data. Our main strategy is to carefully partition a deep neural network to two non-colluding parties. One party performs linear computations on encrypted data utilizing a less complex homo- morphic cryptosystem, while the other executes non-polynomial computations in plaintext but in a privacy-preserved manner. Our extensive experiments on different datasets demonstrate not only stable training without accuracy loss, but also 14 to 35 times speedup compared to the state-of-the-art system.
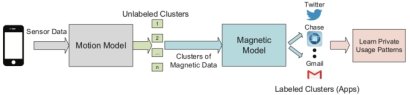
DeepMag
We have discovered a new vulnerability on smartphones due to the malicious use of unsupervised sensor data. We demonstrate that an attacker can train deep Convolutional Neural Networks (CNN) by using magnetometer or orientation data to effectively infer the Apps and their usage information on a smartphone with an accuracy of over 80%. Furthermore, we show that such attacks can become even worse if sophisticated attackers exploit motion sensors to cluster the magnetometer or orientation data, improving the accuracy to as high as 98%. To mitigate such attacks, we develop a noise injection scheme that can effectively reduce the App sniffing accuracy to only 15% and at the same time has negligible effect on benign Apps.
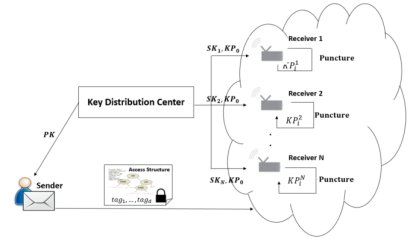
Puncturable Attribute-Based Encryption for Secure Data Delivery in Internet of Things
While the Internet of Things (IoT) is embraced as important tools for efficiency and productivity, it is becoming an increasingly attractive target for cybercriminals. We develop practical Puncturable Attribute Based Encryption schemes that are light-weight and applicable in IoTs. The attribute-based encryption is adopted for fine grained access control. The secret keys are puncturable to revoke the decryption capability for selected messages, recipients, or time periods, thus protecting selected important messages even if the current key is compromised. In contrast to conventional forward encryption, a distinguishing merit of the developed approach is that the recipients can update their keys by themselves without key re-issuing from the key distributor. It does not require frequent communications between IoT devices and the key distribution center, neither does it need deleting components to expunge existing keys to produce a new key. Moreover, we devise a novel approach which efficiently integrates attribute-based key and punctured keys such that the key size is roughly the same as that of the original attribute-based encryption. We also implement the proposed scheme on Raspberry Pi and observe that the computation efficiency of the proposed approach is comparable to the original attribute-based encryption. Both encryption and decryption can be completed within tens of milliseconds.
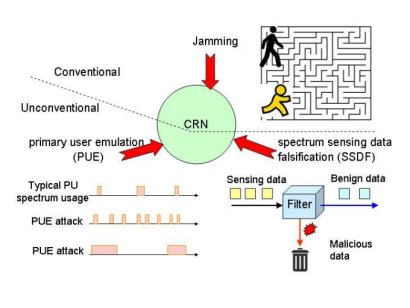
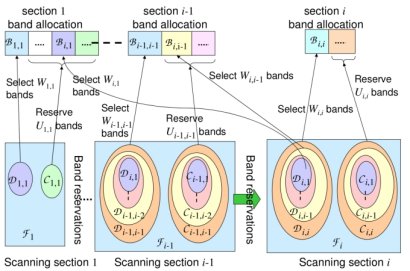
Wireless communications play a key role in both the national economy and our everyday life. However, the radio spectrum used by wireless communications is a limited and extremely valuable natural resource, and is being exhausted due to inefficient allocation. This spectrum scarcity problem has motivated the development of the disruptive cognitive radio and spectrum sharing technologies. The powerful capability of cognitive radio to reconfigure the waveform, and the dynamic manner of spectrum access raise two new security threats to cognitive radio networks, primary user emulation (PUE) and spectrum sensing data falsification (SSDF). A malicious user can launch PUE attacks to cause denial of service (DoS) to secondary users, such that the network performance is significantly degraded.
In collaborative spectrum sensing, a fusion node determines the availability of a channel based on sensing data from other nodes. A malicious user can launch an SSDF attack, i.e., sending false sensing data to mislead the fusion node, which would cause either DoS to secondary users, or harmful interference to primary users.
We are designing effective countermeasure algorithms and mechanisms to address the PUE and SSDF attacks to build secure cognitive radio networks.
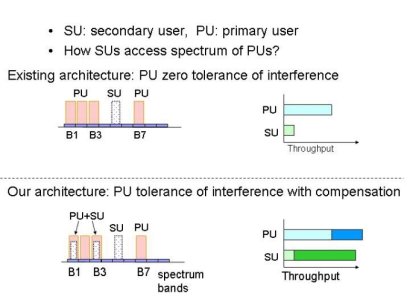
The existing architecture of cognitive radio networks fails to offer incentives to primary users. Hence, secondary users have to conduct spectrum sensing extensively and behave conservatively, which results in large overhead, and a much lower spectrum utilization than expected. Moreover, the existing architecture is vulnerable to the PUE and SSDF attacks. Together, these two issues can reduce the benefit of cognitive radio networks to a marginal level.
Guided by the theories of network coding and dirty paper coding, we are designing new cognitive radio network architectures to incentivize primary users to cooperate with secondary users for spectrum sharing, and relieve the PUE and SSDF attacks, such that both the performance of both primary users and secondary users are dramatically improved.
Furthermore, capitalizing on the recent evolution of spectrum policies, we am designing a novel architecture termed on-demand spectrum access (ODSA), which eliminates the PUE and SSDF attacks and enables users to securely and efficiently share spectrum.
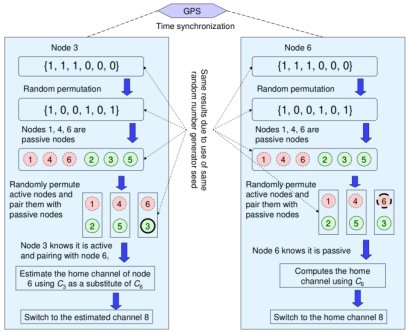
Rendezvous refers to how a transmitter finds the channel of a receiver. In traditional wireless networks such as WiFi, this is a trivial problem, because all nodes are on the same channel. However, it is a totally different story for cognitive radio networks.
In cognitive radio networks, the secondary user or cognitive radio nodes typically operate on different channels due to the dynamic and spatially heterogeneous availability of channels. This situation raises a challenge for MAC Protocols: how do two nodes rendezvous? Many studies assumed using a common control channel. However, this is vulnerable to jamming and traffic congestion.
We are devising proactive anti-jamming rendezvous algorithms, such that cognitive radio nodes are able to proactively find the peers, to achieve efficient, lightweight, and near-optimal rendezvous.
The powerful capability of cognitive radio to reconfigure the waveform, and the dynamic manner of spectrum access raise two new security threats to cognitive radio networks, primary user emulation (PUE) and spectrum sensing data falsification (SSDF). A malicious user can launch PUE attacks to cause denial of service (DoS) to secondary users, such that the network performance is significantly degraded.
In collaborative spectrum sensing, a fusion node determines the availability of a channel based on sensing data from other nodes. A malicious user can launch an SSDF attack, i.e., sending false sensing data to mislead the fusion node, which would cause either DoS to secondary users, or harmful interference to primary users.
We are designing effective countermeasure algorithms and mechanisms to address the PUE and SSDF attacks to build secure cognitive radio networks.
Lab location: 232 Kaufman Hall
Lab phone: 757-683-3470
CCNI Lab in the News
ODU awarded $1 million from the National Science Foundation to help support high-achieving students in cybersecurity program.
Backdoor Detection, Mitigation, and Prevention in Deep Learning Models
NSA, 2021 - 2023, Co-PI
A Development and Experimental Environment for Privacypreserving and Secure (DEEPSECURE) Machine Learning Research
NSF, 2021 - 2024, Co-PI
Blockchain-based Deep Learning Management to Enable Smart NextG Wireless Networks
CCI, 2022 - 2023, Co-PI
Distributed Online Intrusion Detection System for IoT devices via Power Side-channel Auditing
CCI, 2022 - 2023, Co-PI
Beamforming Optimization for 5G and Beyond
CCI, 2021 - 2022, PI
Secure Distributed Digital Manufacturing
ONR, 2018 - 2019, Co-PI
Building a THz Testbed to Expand CCI 5G Testbed for 6G Research
CCI, 2021 - 2022, PI
Comprehensive Assessment and Diagnostics for Federated AI Algorithms in Cyber Physical Systems
CCI, 2021 - 2022, Co-PI
DeepPOSE: Securing Transportation Systems from GPS Spoofing Attacks
CCI, 2020 - 2021, PI
Deep Learning Driven Cybersecurity Research in a Multidisciplinary Environment
NSF, 2019 - 2022, PI
Hampton Roads NROTC Consortium Midshipman Cyber Research and Training
ONR, 2020 - 2021, Co-PI
Improving the Success of Low-Income Students in a Cybersecurity Program
NSF, 2018 - 2023, PI
A Beamforming Optimization Framework for Large Scale mmWave Networks
NSF, 2017 - 2019, PI
Training Cyber Talents for DoD Workforce
NSA, 2021 - 2022, PI
Preparing Tomorrow’s Heroes to Secure the Cyberspace
NSA, 2019 - 2020, PI
Planning Grant: Engineering Research Center for Safe and Secure Artificial Intelligence Solutions (SAIS)
NSA, 2018 - 2020, Co-PI
NeTS: On-Demand Spectrum Access: Application-Oriented Dynamic Spectrum Access
NSF, 2013 - 2018, PI
NeTS-WN: Toward High Performance Mesh Networks
NSF, 2007 - 2010, PI
NSA, 2021 - 20222, PI
Cybersecurity Research in a Multidisciplinary Environment
NSF, 2017 - 2020, PI
Preparing Tomorrow’s Heroes to Secure the Cyberspace
NSA, 2016 - 2017, Co-PI
NeTS: Collaborative Research: Learning to help: Trading spectrum ownership for performance
NSF, 2010 - 2013, PI
Implementation of Vertically Integrated Curriculum for Cognitive Radio Communications
NSF, 2009 - 2011, Co-PI